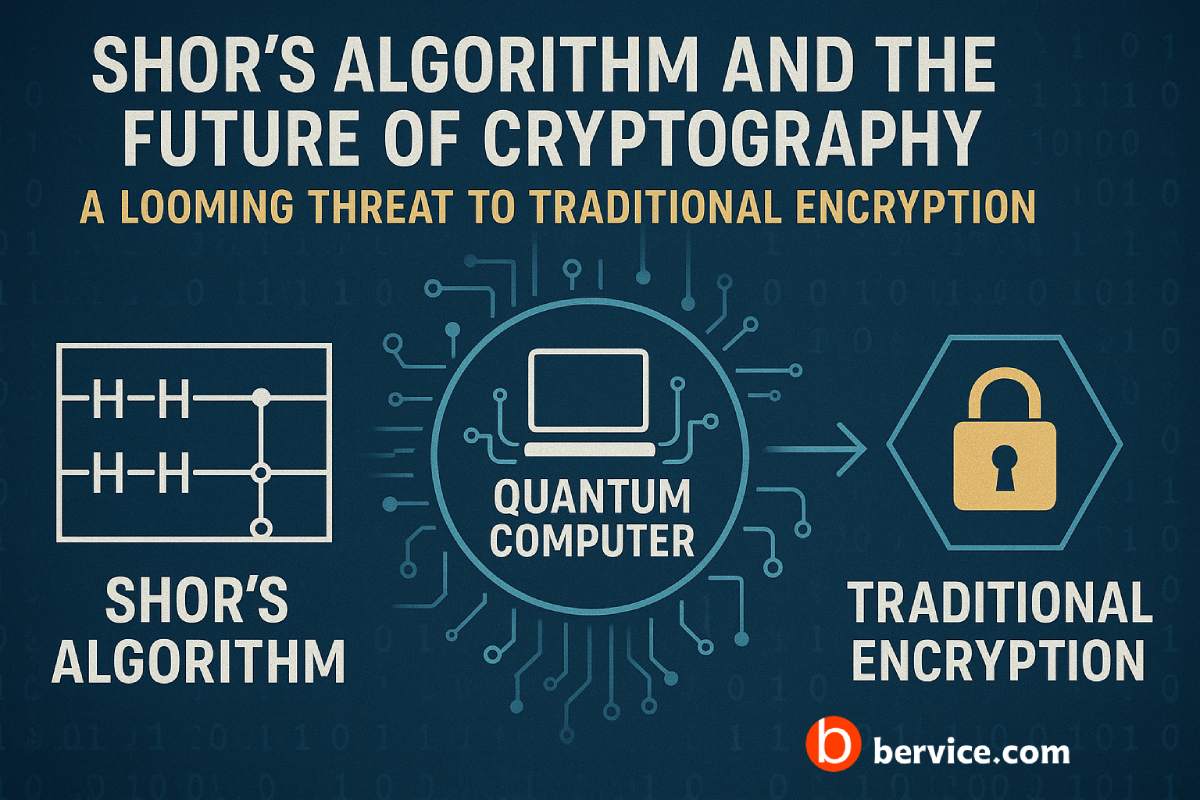
Post-Quantum Cryptography (PQC) refers to cryptographic algorithms that are designed to be secure against the potential threats posed by quantum computers. Quantum computers, once fully developed, are expected to break the security of many widely used cryptographic protocols, such as RSA and ECC (Elliptic Curve Cryptography), which rely on the difficulty of factoring large numbers or solving discrete logarithms—problems that quantum algorithms like Shor’s algorithm can solve in polynomial time. This poses a serious threat to the confidentiality and integrity of digital communications, financial transactions, and other secure systems.
Why is PQC Important?
Currently, many of the cryptographic systems in use today are based on mathematical problems that quantum computers could potentially solve efficiently. If quantum computers become sufficiently powerful, they could easily break many of the existing encryption methods that protect sensitive data. As a result, the development of post-quantum cryptographic algorithms is crucial to ensure that data remains secure in a future where quantum computing is a practical reality.
Key Aspects of PQC:
- Quantum Resistance: PQC aims to provide security even in the presence of quantum computers. It focuses on developing cryptographic algorithms that do not rely on the mathematical problems vulnerable to quantum attacks.
- Standardization Efforts: The National Institute of Standards and Technology (NIST) has been actively working on the standardization of post-quantum cryptographic algorithms. They have organized a multi-phase process to evaluate various quantum-resistant algorithms, with the goal of selecting those that offer the best balance of security, efficiency, and ease of implementation.
- Types of Algorithms:
- Lattice-Based Cryptography: Algorithms based on the hardness of lattice problems (e.g., Learning With Errors (LWE) problem) are considered strong candidates for PQC.
- Code-Based Cryptography: These algorithms are based on error-correcting codes, and they have been studied for a long time as potential quantum-resistant methods.
- Multivariate Polynomial Cryptography: These schemes rely on the difficulty of solving systems of multivariate quadratic equations.
- Hash-Based Cryptography: Digital signature schemes based on hash functions, which are believed to be resistant to quantum attacks.
- Isogeny-Based Cryptography: This involves the difficulty of finding isogenies between elliptic curves, and is considered a promising area for PQC.
Challenges in PQC:
- Efficiency: Some post-quantum algorithms can be slower and require more computational resources compared to traditional cryptographic systems.
- Interoperability: Transitioning to PQC solutions must be done carefully to ensure that current systems and applications remain secure and functional during the transition period.
- Implementation: Many of the proposed PQC algorithms are still undergoing extensive testing and review to determine how well they perform in real-world conditions, including on hardware platforms and in low-resource environments.
The Future of Post-Quantum Cryptography:
As quantum computers evolve, it is anticipated that PQC will become an essential component of secure systems. Organizations, governments, and businesses must start preparing for this transition by developing strategies to incorporate quantum-resistant algorithms into their existing infrastructure. The standardization and adoption of PQC will likely occur in stages, with legacy systems coexisting alongside new quantum-resistant solutions for some time.
In conclusion, Post-Quantum Cryptography is vital for the future of cybersecurity, ensuring that sensitive information remains protected in a world where quantum computing could otherwise break traditional cryptographic schemes. It represents a critical area of research and development that will shape the security landscape for years to come.
Connect with us : https://linktr.ee/bervice