As quantum computers evolve, they present a significant threat to current cryptographic methods that are widely used for securing communications and data. Quantum computing’s potential to solve complex problems exponentially faster than classical computers means that conventional encryption techniques, such as RSA and ECC, are vulnerable to being broken. This is where quantum cryptography steps in, offering solutions to counter these threats and ensure data security in the age of quantum computing.
1. Quantum Key Distribution (QKD)
Quantum Key Distribution (QKD) is one of the most promising methods of securing communication in the face of quantum computing. QKD uses the principles of quantum mechanics, specifically quantum superposition and entanglement, to generate and share cryptographic keys between two parties.
How It Works:
- QKD relies on the transmission of quantum bits (qubits) that are encoded in quantum states. Any attempt by a third party to intercept or measure these qubits causes a disturbance in the system, which can be detected by the sender and receiver.
- This ensures that the key exchange is secure, even if a quantum computer is used by an attacker. The most commonly used QKD protocol is BB84, which was proposed by Charles Bennett and Gilles Brassard in 1984. Other protocols, like E91 (based on quantum entanglement), are also under consideration.
Strengths:
- Provides a theoretically unbreakable communication channel if implemented correctly.
- Detects eavesdropping automatically due to the “no-cloning” theorem in quantum mechanics.
Challenges:
- Requires a secure physical infrastructure for the transmission of quantum states (e.g., fiber optics or free-space channels).
- The technology is still in the development phase for large-scale practical use.
2. Post-Quantum Cryptography (PQC)
Post-Quantum Cryptography (PQC) refers to cryptographic algorithms that are designed to be secure against the capabilities of quantum computers. While QKD uses quantum properties for key distribution, PQC focuses on creating algorithms that do not rely on quantum mechanics for their security, making them suitable for classical computers today while remaining resistant to quantum-based attacks in the future.
Common Post-Quantum Cryptographic Algorithms:
- Lattice-based cryptography: This includes schemes like NTRU and Ring-LWE. These algorithms rely on the hardness of lattice problems, which are believed to be hard even for quantum computers to solve.
- Code-based cryptography: Algorithms like McEliece are based on the difficulty of decoding a random linear code.
- Hash-based cryptography: Such as Merkel trees, these algorithms rely on the one-wayness of hash functions, which are difficult for quantum computers to break.
- Multivariate quadratic equations (MQ): These schemes rely on the difficulty of solving systems of multivariate quadratic equations.
Strengths:
- Can be implemented on classical systems, making them immediately deployable for transition to post-quantum secure systems.
- NIST (National Institute of Standards and Technology) is actively working on standardizing post-quantum algorithms to replace vulnerable classical algorithms like RSA and ECC.
Challenges:
- The algorithms often require larger key sizes and more computational power, which may be a drawback in environments with limited resources.
- Transitioning from classical to post-quantum cryptography requires significant changes in infrastructure.
3. Quantum Secure Authentication (QSA)
Quantum Secure Authentication (QSA) methods aim to provide secure authentication mechanisms that are resistant to quantum computer attacks. Traditional authentication mechanisms, like password-based systems, are vulnerable to quantum computers’ ability to solve problems like discrete logarithms or factorization in polynomial time.
Example Methods:
- Quantum Signature Schemes: These schemes leverage quantum mechanics to generate unforgeable digital signatures. One such method is Quantum Digital Signatures (QDS), where signatures are created using quantum states, ensuring that any modification to the signature would be detectable due to the no-cloning theorem.
- Quantum Random Number Generation (QRNG): QRNG uses quantum processes, such as photon behavior, to generate truly random numbers for cryptographic operations, making it harder for quantum computers to predict or reproduce the number sequences.
Strengths:
- Provides robust security against quantum computer attacks by exploiting quantum properties.
- Can be used to secure both user authentication and device authentication in IoT and other modern systems.
Challenges:
- The integration of QSA into existing systems is still at a nascent stage.
- Practical deployment may require significant investment in quantum-safe hardware.
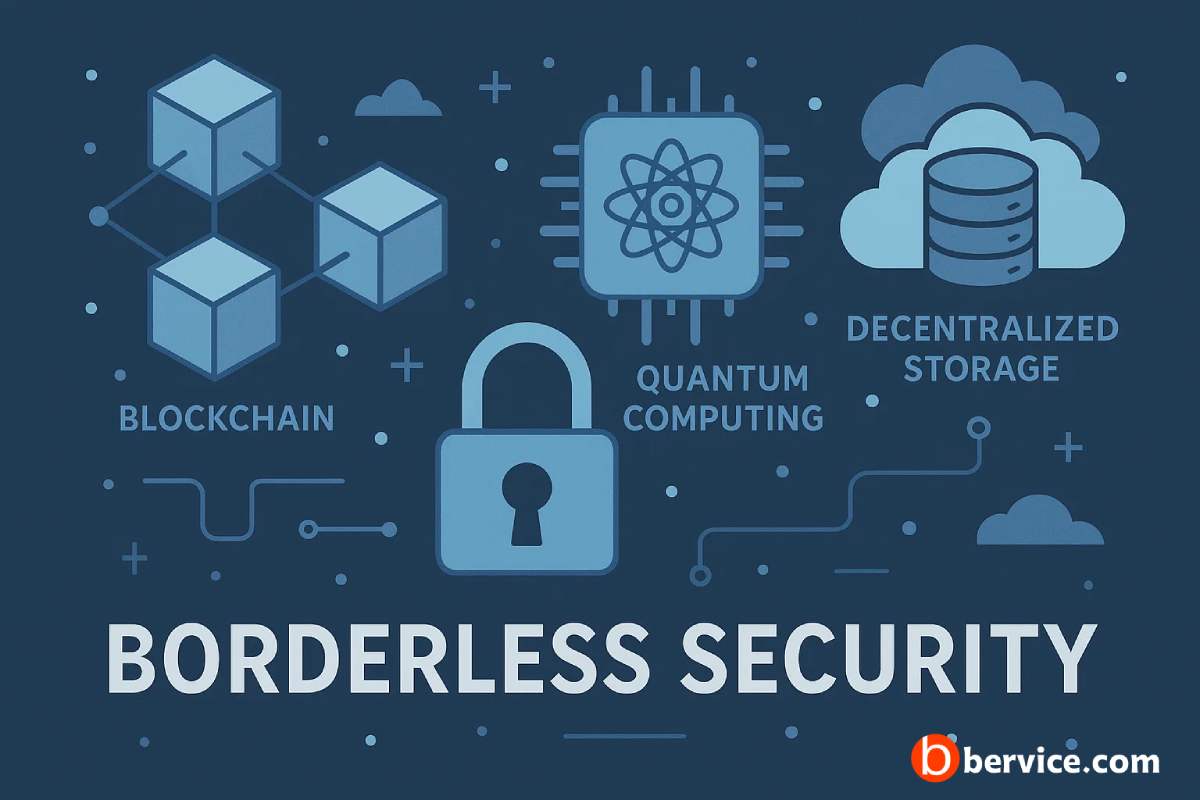
4. Quantum-Resistant Blockchain
Blockchain technology has found its application in cryptocurrencies, financial transactions, and supply chain management. However, with the advent of quantum computers, the cryptographic security of traditional blockchains, which depend on elliptic curve cryptography (ECC), is at risk.
Quantum-resistant blockchains are being developed using post-quantum cryptographic algorithms. These blockchains use quantum-safe digital signatures to ensure the integrity and security of data stored on the blockchain, preventing quantum computers from stealing assets or altering records.
Key Technologies:
- Lattice-based encryption: Integrating lattice-based algorithms into blockchain protocols to secure transactions and data.
- Hash-based digital signatures: Adopting hash-based signature schemes such as Merkel signatures to replace ECC in the blockchain.
Strengths:
- Quantum-resistant blockchains can future-proof cryptocurrency systems, ensuring they remain secure against quantum attacks.
- They can be deployed as an upgrade to current blockchain systems or as part of entirely new blockchain protocols.
Challenges:
- Significant upgrades to blockchain infrastructure are required to support quantum-resistant algorithms.
- There is a need for cross-industry collaboration to develop and implement these technologies.
Conclusion
As quantum computers continue to advance, the traditional methods of securing digital data and communication are becoming increasingly vulnerable. However, the development of quantum cryptography methods such as Quantum Key Distribution (QKD), Post-Quantum Cryptography (PQC), Quantum Secure Authentication (QSA), and Quantum-Resistant Blockchain offers a pathway to secure systems in the quantum computing era. While these technologies are still evolving and require further research and development, they represent the best hope for maintaining data security and privacy in a world where quantum computers will eventually become a reality.
As we transition towards a quantum-safe future, businesses, governments, and researchers must work together to prepare for the upcoming quantum revolution by investing in quantum-resistant technologies and adapting to the evolving threat landscape.
Connect with us : https://linktr.ee/bervice